Web
News
How Thales Protects Online Retail Sites from AI-Driven Bots during Holiday Shopping Season
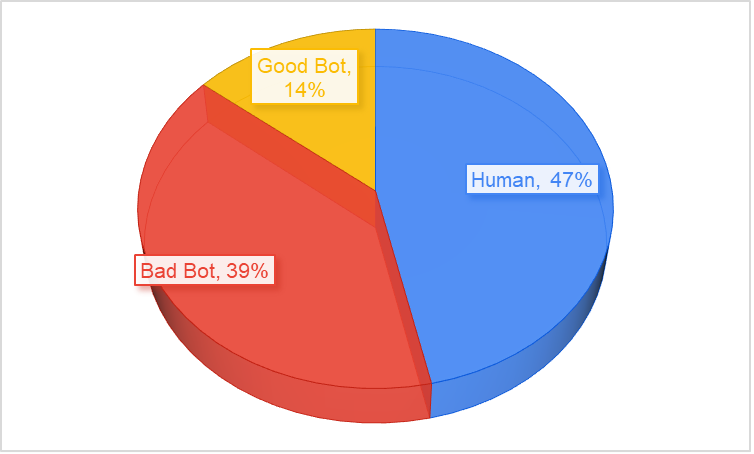 4+ day, 4+ hour ago (412+ words) Home " Cybersecurity " Application Security " How Thales Protects Online Retail Sites from AI-Driven Bots during Holiday Shopping Season Every November and December, online retailers gear up for their biggest revenue surge of the year. But while the traffic and transactions climb, so does the threat level. Cybercriminals know exactly when customer activity (and the pressure on retail systems) is at its highest and they're automating their attacks to exploit it. Chart based on data from November 2024 to November 2025 Retailers going into peak retail season without strong bot- and account-abuse defences are exposing a key part of their business to automated fraud and exploitation. Retailers often focus on obvious fraud vectors (payment fraud, card testing), but bots bring subtler, higher-volume risks that can erode margins, trust, and availability: These are not threats to be taken lightly. Modern bots imitate human behaviour (headless…...
4+ day, 4+ hour ago (412+ words) Home " Cybersecurity " Application Security " How Thales Protects Online Retail Sites from AI-Driven Bots during Holiday Shopping Season Every November and December, online retailers gear up for their biggest revenue surge of the year. But while the traffic and transactions climb, so does the threat level. Cybercriminals know exactly when customer activity (and the pressure on retail systems) is at its highest and they're automating their attacks to exploit it. Chart based on data from November 2024 to November 2025 Retailers going into peak retail season without strong bot- and account-abuse defences are exposing a key part of their business to automated fraud and exploitation. Retailers often focus on obvious fraud vectors (payment fraud, card testing), but bots bring subtler, higher-volume risks that can erode margins, trust, and availability: These are not threats to be taken lightly. Modern bots imitate human behaviour (headless…...
Etsy Stops Unwanted Traffic & Reduces Computing Costs with DataDome & Google
 4+ mon, 4+ week ago (412+ words) Home " Security Bloggers Network " Etsy Stops Unwanted Traffic & Reduces Computing Costs with DataDome & Google Etsy, the global destination for unique and creative goods, wanted to gain more control over scrapers and other types of bots. Using DataDome's AI-powered solution, they reduced computing costs and improved data accuracy by filtering bot traffic. This has enabled Etsy to protect its community of millions of buyers and sellers. However, as Etsy grew into a larger marketplace, more bots showed interest in the platform. At the same time, Etsy was improving the customer experience with more and more machine learning, which can increase the amount of servers needed to serve pages. As a cost-conscious company, they wanted to stay in control of how resources were used. Etsy analyzed their data and estimated that, if left unmanaged, scrapers could possibly account for about 1% of Etsy's…...
4+ mon, 4+ week ago (412+ words) Home " Security Bloggers Network " Etsy Stops Unwanted Traffic & Reduces Computing Costs with DataDome & Google Etsy, the global destination for unique and creative goods, wanted to gain more control over scrapers and other types of bots. Using DataDome's AI-powered solution, they reduced computing costs and improved data accuracy by filtering bot traffic. This has enabled Etsy to protect its community of millions of buyers and sellers. However, as Etsy grew into a larger marketplace, more bots showed interest in the platform. At the same time, Etsy was improving the customer experience with more and more machine learning, which can increase the amount of servers needed to serve pages. As a cost-conscious company, they wanted to stay in control of how resources were used. Etsy analyzed their data and estimated that, if left unmanaged, scrapers could possibly account for about 1% of Etsy's…...
 2+ week, 4+ day ago (279+ words) Former DoJ attorney John Carlin writes about hackback, which he defines thus: "A hack back is a type of cyber response that incorporates a counterattack designed to proactively engage with, disable, or collect evidence about an attacker. Although hack backs can take on various forms, they are'by definition'not passive defensive measures." His conclusion: As the law currently stands, specific forms of purely defense measures are authorized so long as they affect only the victim's system or data. At the other end of the spectrum, offensive measures that involve accessing or otherwise causing damage or loss to the hacker's systems are likely prohibited, absent government oversight or authorization. And even then parties should proceed with caution in light of the heightened risks of misattribution, collateral damage, and retaliation... The post On Hacking Back appeared first on Security Boulevard. Home " Security Bloggers…...
2+ week, 4+ day ago (279+ words) Former DoJ attorney John Carlin writes about hackback, which he defines thus: "A hack back is a type of cyber response that incorporates a counterattack designed to proactively engage with, disable, or collect evidence about an attacker. Although hack backs can take on various forms, they are'by definition'not passive defensive measures." His conclusion: As the law currently stands, specific forms of purely defense measures are authorized so long as they affect only the victim's system or data. At the other end of the spectrum, offensive measures that involve accessing or otherwise causing damage or loss to the hacker's systems are likely prohibited, absent government oversight or authorization. And even then parties should proceed with caution in light of the heightened risks of misattribution, collateral damage, and retaliation... The post On Hacking Back appeared first on Security Boulevard. Home " Security Bloggers…...
 7+ mon, 2+ week ago (17+ words) test The post test-SB3 appeared first on Security Boulevard. Home " Social - X " test-SB3...
7+ mon, 2+ week ago (17+ words) test The post test-SB3 appeared first on Security Boulevard. Home " Social - X " test-SB3...
SafeBreach 2024 Year in Review: Reflections from Co-Founder & CEO Guy Bejerano
 10+ mon, 2+ week ago (697+ words) Home " Security Bloggers Network " SafeBreach 2024 Year in Review: Reflections from Co-Founder & CEO Guy Bejerano Happy new year! 2025 is underway and the SafeBreach team is off to a strong start after a record-breaking 2024. We are keenly focused on the vision, goals, and opportunities that lie ahead in the new year'some of which we are excited to share in much more detail soon." Most notably, we ended the year with a record-breaking quarter for enterprise sales in Q4. As we start 2025, some of the largest enterprises in the world have chosen SafeBreach as their breach and attack simulation (BAS) vendor of choice:" I am grateful for the trust these organizations'and all of our clients'have placed in us. It serves as our motivation as we work tirelessly to provide enterprise-grade technology solutions and solidifies our position as the leading enterprise BAS solution on the…...
10+ mon, 2+ week ago (697+ words) Home " Security Bloggers Network " SafeBreach 2024 Year in Review: Reflections from Co-Founder & CEO Guy Bejerano Happy new year! 2025 is underway and the SafeBreach team is off to a strong start after a record-breaking 2024. We are keenly focused on the vision, goals, and opportunities that lie ahead in the new year'some of which we are excited to share in much more detail soon." Most notably, we ended the year with a record-breaking quarter for enterprise sales in Q4. As we start 2025, some of the largest enterprises in the world have chosen SafeBreach as their breach and attack simulation (BAS) vendor of choice:" I am grateful for the trust these organizations'and all of our clients'have placed in us. It serves as our motivation as we work tirelessly to provide enterprise-grade technology solutions and solidifies our position as the leading enterprise BAS solution on the…...
NDSS 2025 - SCAMMAGNIFIER: Piercing The Veil Of Fraudulent Shopping Website Campaigns
 3+ week, 1+ day ago (453+ words) SESSION Session 2C: Phishing & Fraud 1 Authors, Creators & Presenters: Marzieh Bitaab (Arizona State University), Alireza Karimi (Arizona State University), Zhuoer Lyu (Arizona State University), Adam Oest (Amazon), Dhruv Kuchhal (Amazon), Muhammad Saad (X Corp.), Gail-Joon Ahn (Arizona State University), Ruoyu Wang (Arizona State University), Tiffany Bao (Arizona State University), Yan Shoshitaishvili (Arizona State University), Adam Doup" (Arizona State University) PAPER SCAMMAGNIFIER: Piercing the Veil of Fraudulent Shopping Website Campaigns In an evolving digital environment under perpetual threat from cybercriminals, phishing remains a predominant concern. However, there is a shift towards fraudulent shopping websites---fraudulent websites offering bogus products or services while mirroring the user experience of legitimate shopping websites. A key open question is how important fraudulent shopping websites in the cybercrime ecosystem are? This study introduces a novel approach to detecting and analyzing fraudulent shopping websites through large-scale analysis and collaboration…...
3+ week, 1+ day ago (453+ words) SESSION Session 2C: Phishing & Fraud 1 Authors, Creators & Presenters: Marzieh Bitaab (Arizona State University), Alireza Karimi (Arizona State University), Zhuoer Lyu (Arizona State University), Adam Oest (Amazon), Dhruv Kuchhal (Amazon), Muhammad Saad (X Corp.), Gail-Joon Ahn (Arizona State University), Ruoyu Wang (Arizona State University), Tiffany Bao (Arizona State University), Yan Shoshitaishvili (Arizona State University), Adam Doup" (Arizona State University) PAPER SCAMMAGNIFIER: Piercing the Veil of Fraudulent Shopping Website Campaigns In an evolving digital environment under perpetual threat from cybercriminals, phishing remains a predominant concern. However, there is a shift towards fraudulent shopping websites---fraudulent websites offering bogus products or services while mirroring the user experience of legitimate shopping websites. A key open question is how important fraudulent shopping websites in the cybercrime ecosystem are? This study introduces a novel approach to detecting and analyzing fraudulent shopping websites through large-scale analysis and collaboration…...
NDSS 2025 - The Discriminative Power Of Cross-layer RTTs In Fingerprinting Proxy Traffic
 2+ week, 1+ day ago (439+ words) SESSION Session 3A: Network Security 1 Authors, Creators & Presenters: Diwen Xue (University of Michigan), Robert Stanley (University of Michigan), Piyush Kumar (University of Michigan), Roya Ensafi (University of Michigan) ----- PAPER ----- The Discriminative Power of Cross-layer RTTs in Fingerprinting Proxy Traffic The escalating global trend of Internet censorship has necessitated an increased adoption of proxy tools, especially obfuscated circumvention proxies. These proxies serve a fundamental need for access and connectivity among millions in heavily censored regions. However, as the use of proxies expands, so do censors' dedicated efforts to detect and disrupt such circumvention traffic to enforce their information control policies. In this paper, we bring out the presence of an inherent fingerprint for detecting obfuscated proxy traffic. The fingerprint is created by the misalignment of transport- and application-layer sessions in proxy routing, which is reflected in the discrepancy in Round Trip Times…...
2+ week, 1+ day ago (439+ words) SESSION Session 3A: Network Security 1 Authors, Creators & Presenters: Diwen Xue (University of Michigan), Robert Stanley (University of Michigan), Piyush Kumar (University of Michigan), Roya Ensafi (University of Michigan) ----- PAPER ----- The Discriminative Power of Cross-layer RTTs in Fingerprinting Proxy Traffic The escalating global trend of Internet censorship has necessitated an increased adoption of proxy tools, especially obfuscated circumvention proxies. These proxies serve a fundamental need for access and connectivity among millions in heavily censored regions. However, as the use of proxies expands, so do censors' dedicated efforts to detect and disrupt such circumvention traffic to enforce their information control policies. In this paper, we bring out the presence of an inherent fingerprint for detecting obfuscated proxy traffic. The fingerprint is created by the misalignment of transport- and application-layer sessions in proxy routing, which is reflected in the discrepancy in Round Trip Times…...
SaaS Black Friday deals For Developer 2025
1+ week, 3+ day ago (1198+ words) Home " Security Bloggers Network " SaaS Black Friday deals For Developer 2025 The biggest SaaS savings of 2025 are here. Discover the Best Passwordless Authentication Black Friday Deals 2025" early and make smarter decisions for your business. MojoAuth delivers passwordless authentication, so users log in with email or OTP instead of passwords. Developers integrate their SDKs to add secure, frictionless sign-in across web and mobile apps. The service enforces strong security standards while lowering login drop-offs. Companies implement it to reduce credential theft and boost conversions. SSOJet secures and centralises user sign-on across your apps with single sign-on (SSO). It supports enterprise protocols and integrates with popular identity providers to simplify access management. Admins configure policies, monitor logins, and reduce password-related support tickets. Teams rely on it to improve security and user convenience. Gracker.ai helps cybersecurity marketers find keywords, generate blog content, and…...
News alert: 360 Privacy secures $36M to deliver turnkey digital executive protection platform
 8+ mon, 2+ week ago (528+ words) Nashville, TN " Mar. 11, 2025360 Privacy, a leading digital executive protection platform, today announced that it has secured a $36 million growth equity investment fromFTV Capital, a sector-focused growth equity firm with a successful " (more") The post News alert: 360 Privacy secures $36M to deliver turnkey digital executive protection platform first appeared on The Last Watchdog. The post News alert: 360 Privacy secures $36M to deliver turnkey digital executive protection platform appeared first on Security Boulevard. Nashville, TN " Mar. 11, 2025 " 360 Privacy, a leading digital executive protection platform, today announced that it has secured a $36 million growth equity investment from FTV Capital, a sector-focused growth equity firm with a successful track record of investing across the enterprise technology landscape. In 2024, the average cost of a data breach reached $4.88 million, with nearly half (46 percent) of all breaches involving personally identifiable information (PII), such as addresses, social security numbers, credit card…...
8+ mon, 2+ week ago (528+ words) Nashville, TN " Mar. 11, 2025360 Privacy, a leading digital executive protection platform, today announced that it has secured a $36 million growth equity investment fromFTV Capital, a sector-focused growth equity firm with a successful " (more") The post News alert: 360 Privacy secures $36M to deliver turnkey digital executive protection platform first appeared on The Last Watchdog. The post News alert: 360 Privacy secures $36M to deliver turnkey digital executive protection platform appeared first on Security Boulevard. Nashville, TN " Mar. 11, 2025 " 360 Privacy, a leading digital executive protection platform, today announced that it has secured a $36 million growth equity investment from FTV Capital, a sector-focused growth equity firm with a successful track record of investing across the enterprise technology landscape. In 2024, the average cost of a data breach reached $4.88 million, with nearly half (46 percent) of all breaches involving personally identifiable information (PII), such as addresses, social security numbers, credit card…...
 1+ mon, 2+ week ago (306+ words) Home " Security Bloggers Network " Inside the F5 Breach Below, we take a detailed look at what actually happened, why it is serious, and what security leaders should be thinking about now. For organizations that use F5 products or operate in sectors that depend on layered infrastructure security, the implications of this breach go beyond the technical and raise strategic concerns about long-term exposure and trust. CISA issued Emergency Directive 26-01 on the same day F5 disclosed the breach, requiring federal civilian agencies to take immediate steps to secure their environments. These steps include identifying all F5 appliances on federal networks, applying the latest available patches, isolating or removing public access to management interfaces, and submitting detailed reports within 72 hours. Security teams in the private sector should view CISA's directive as a practical benchmark for their own incident response. It reflects a conservative, defense-first approach to…...
1+ mon, 2+ week ago (306+ words) Home " Security Bloggers Network " Inside the F5 Breach Below, we take a detailed look at what actually happened, why it is serious, and what security leaders should be thinking about now. For organizations that use F5 products or operate in sectors that depend on layered infrastructure security, the implications of this breach go beyond the technical and raise strategic concerns about long-term exposure and trust. CISA issued Emergency Directive 26-01 on the same day F5 disclosed the breach, requiring federal civilian agencies to take immediate steps to secure their environments. These steps include identifying all F5 appliances on federal networks, applying the latest available patches, isolating or removing public access to management interfaces, and submitting detailed reports within 72 hours. Security teams in the private sector should view CISA's directive as a practical benchmark for their own incident response. It reflects a conservative, defense-first approach to…...